Authentication, identification, and authorization
Quite an important task in the development of websites and web applications is restricting access to certain sections of the site, such as the admin panel. In theory, this is a rather complex process, consisting of three components - authentication, identification, and authorization.
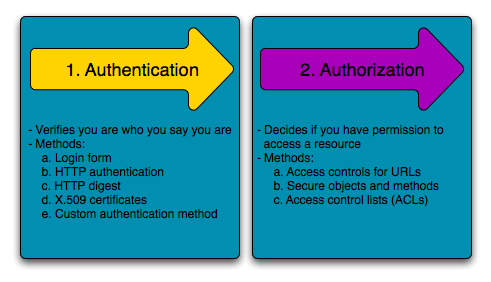
Right after entering the credentials (this can be a username/password pair, one-time password, access token, md5 hash, certificate, and many more), the authentication process begins. It involves the verification of authenticity. For example, matching the user's username/password with the corresponding account in the database, checksum verification of a file, and so on.
In general, to perform authentication, you either need to know something (such as a password), have an authentication device (like your smartphone in many modern electronic banking systems), or possess some unique biometric data - fingerprints, facial features, voice, iris, and so on.
If the authentication process succeeds, the next step is identification. The purpose of identification is to obtain the user's identifier in the system. It could be their ID, unique username, email, and so on. This is something the website manipulates.
And finally, after all of this, comes the authorization. The essence of authorization is to grant the user certain privileges. For example, administrator rights, user rights, anonymous (unauthenticated) user rights.
Often, in PHP scripts, there is no clear separation between the first and second stage, or even all three. In the simplest case, these actions can be done with a single database query.
However, what has been written here is important for understanding the security system in more complex products and frameworks in particular.
Thus, we now know what authentication, identification, and authorization mean in the context of website development.